Here's What You Need To Do If Your Personal Data Has Been Leaked, Hacked, or Breached
October 31, 2023
Return to Learning Center
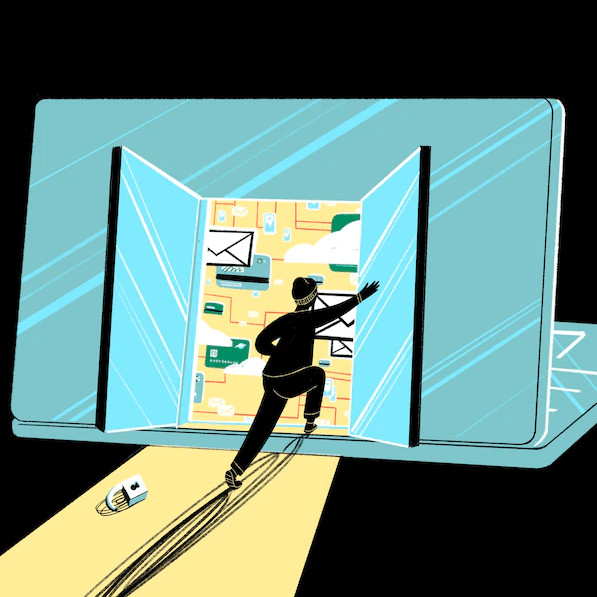
Hacks and data breaches have become a persistent part of life in the 21st century, and the proof is in the news. Ransomware has crippled towns and cities, T-Mobile lost control over millions of people's personal information, Apple recently released software updates to plug security holes and Twitch had all of its source code - along with information about streamers' pay - leaked.
New research from the Identity Theft Resource Center shows that the number of publicly reported data breaches from the beginning of 2021 to the end of September totaled 1,291, a 17% increase from the total reported throughout all of 2020.
Too many people find out they've been affected only after the damage has already been done. If you're vigilant and lucky you might be able to stop a hack before it happens. And if you find yourself the victim of a hack or data breach, or think you might be, here's our guide to the steps you should take immediately.
DHS defines personally identifiable information or PII as any information that permits the identity of an individual to be directly or indirectly inferred, including any information that is linked or linkable to that individual, regardless of whether the individual is a U.S. citizen, lawful permanent resident, visitor to the U.S., or employee or contractor to the Department.
The best defense against these types of attacks is a solid offense and to be proactive. One critical and important step you can take BEFORE a data breach is to remove your data from data broker sites. This prevents your personal data from being exposed in the first place, even if the data broker site gets hacked or breached.
Also, the loss of Sensitive PII even in an encrypted or password-protected format could become a privacy incident. For instance, if encrypted or password-protected Sensitive PII, along with the "key" or password to access the information, is sent to a person without a "need to know" or to a personal e-mail address, this would be considered a privacy incident.
Change your passwords as soon as you've spotted some of the sketchy behavior we talked about earlier, or the moment you've confirmed that you've been hacked. It's not uncommon for people to reuse the same password across multiple sites and services - if that sounds like you, move fast.
Fixing your passwords is just the start - you'll also want to add another layer of protection. That's where two-factor authentication comes in. The most common form of two-factor authentication - or 2FA - relies on text messages. If you've ever been prompted to punch in a code that gets texted to your phone when logging into a website or service, you already have some experience with 2FA.
Once you've locked down your other accounts, it's time to start trying to recover ones you may have lost control of. Many commonly used services offer a suite of tools to help you verify your identity and regain access to your accounts, but some make it easier than others.
We hope you enjoyed reading this guide and learned something new! Check out our Learning Center to learn more about online privacy and security or consider subscribing to our Online Privacy Service to remove your phone number, name, and address from Google, Bing, Yahoo, and DuckDuckGo search results and hundreds of data broker sites.